network attack vectors
Cloud Load Balancing – Does your provider have what it takes? | Radware. 9 Pics about Cloud Load Balancing – Does your provider have what it takes? | Radware : Cyber Attack Vector Icons - Download Free Vector Art, Stock Graphics, Threat Alert: TCP Amplification Attacks | Radware Blog and also Threat Alert: TCP Amplification Attacks | Radware Blog.
Cloud Load Balancing – Does Your Provider Have What It Takes? | Radware
 blog.radware.com
blog.radware.com
cloud balancing load radware
Phishing By Email Spoofing Internet Concept Illustration 173982 Vector
 www.vecteezy.com
www.vecteezy.com
phishing email spoofing vector illustration internet monitoring concept 1yr dark web vecteezy edit company
Agile, DevOps And Load Balancers: Evolution Of Network Operations
 blog.radware.com
blog.radware.com
agile devops load funds fund automation balancers operations evolution network radware trintech lending direct
Threat Alert: TCP Amplification Attacks | Radware Blog
 blog.radware.com
blog.radware.com
threat radware tcp amplification
Cyber Attack Vector Icons - Download Free Vector Art, Stock Graphics
cyber pictogrammen arame preparada ciberataque lineaire veiligheid vectorified vectoren
Advanced Persistent Threats In 2021: New Threat Angles And Attack
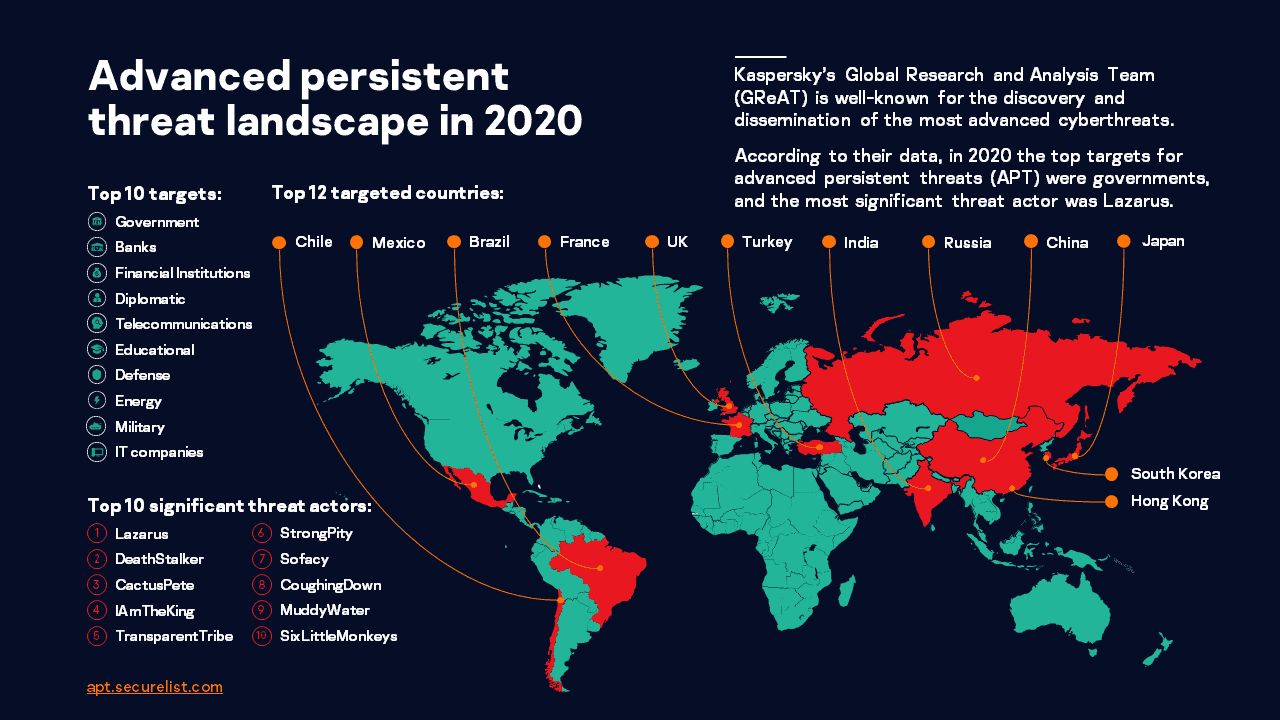 ramarama.my
ramarama.my
threat persistent threats ksb malware securelist ramarama ransomware
Social Engineer Toolkit (SET) Tutorial For Penetration Testers
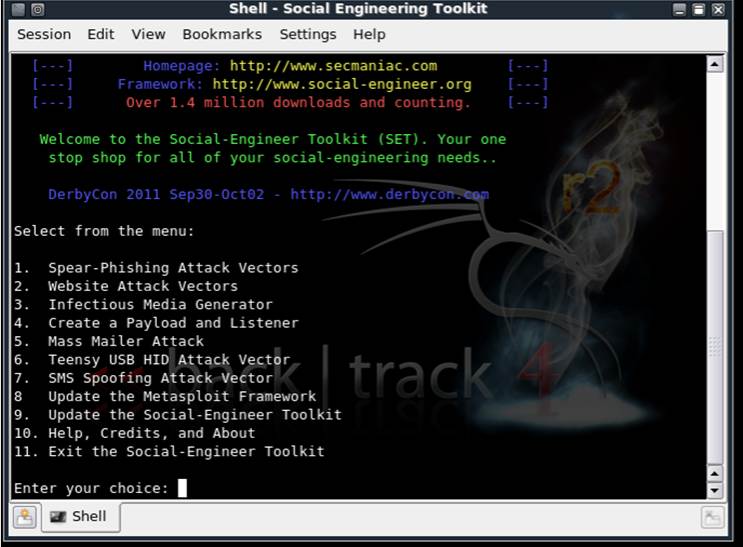 www.computerweekly.com
www.computerweekly.com
social toolkit hacking windows tools engineer engineering opening tutorial testers penetration security techworm
Applying Attack Surface Reduction On Top Of Attack Surface Reduction
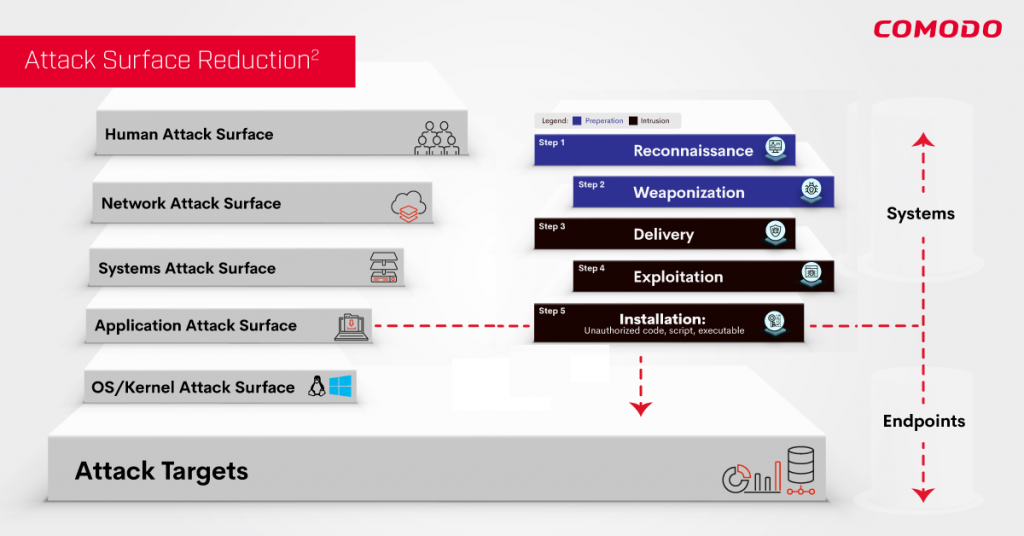 techtalk.comodo.com
techtalk.comodo.com
asr2 comodo lets
ADCollector - A Lightweight Tool To Quickly Extract Valuable
 www.kitploit.com
www.kitploit.com
active directory environment implementation lightweight tool windows defending quickly extract attacking valuable both enumerates identify attack possible vectors give sign
Threat radware tcp amplification. Agile, devops and load balancers: evolution of network operations. Applying attack surface reduction on top of attack surface reduction